(And Don’t Realise Until It’s Too Late)
For most businesses with 10–50 employees, choosing an IT provider feels like a practical decision.
Who’s responsive?
Who’s affordable?
Who can fix things when they break?
On the surface, it’s a procurement exercise.
In reality, it’s something far more serious.
You’re not choosing IT support.
You’re choosing how your business manages risk.
And that’s where most businesses get it wrong.
The Mistake: Treating IT as a Cost, Not a Control
When business owners evaluate IT providers, the conversation usually revolves around:
- Monthly cost
- Response times
- Tools and software
- Cybersecurity “features”
It feels logical. Tangible. Comparable.
But it completely misses the point.
The reason you have IT systems, security controls, and processes in place isn’t just to “keep things running.”
It’s to protect the business, its data, and its directors from regulatory, financial, and reputational risk.
That means your IT provider isn’t just a supplier.
They are part of your governance framework.
The Reality: You Are Accountable—Not Your IT Provider
UK legislation doesn’t care who your IT provider is.
Under laws such as:
- The Companies Act
- The Computer Misuse Act
- The Data Protection Act 2018
…the responsibility sits with you.
The directors.
The business owners.
The decision-makers.
If something goes wrong—a data breach, ransomware attack, or loss of sensitive client data—the question isn’t:
“Who was your IT provider?”
It’s:
“Can you demonstrate that you were managing this risk appropriately?”
And that’s a very different conversation.
The Dangerous Gap: Technology Without Evidence
Here’s where most small businesses become exposed.
They invest in:
- Antivirus
- Firewalls
- Backups
- Email security
They believe they’re “covered.”
But when you look closer, something critical is missing:
Evidence.
- Where is the documentation of risk?
- Where are the policies governing data handling?
- Where is the record of decisions made?
- Where is the proof of monitoring and review?
- Where is the audit trail of control?
Without this, all the technology in the world doesn’t protect you.
Because in the eyes of a regulator, if it’s not evidenced, it didn’t happen.
What Happens After a Breach
Let’s make this real.
A small professional services firm—say 15 people—handles client financial data.
One afternoon, a spreadsheet is sent to the wrong recipient.
Names. Salaries. Personal data.
A breach.
At this point, many business owners assume the key question will be:
“How did this happen?”
But when the Information Commissioner's Office gets involved, the conversation quickly shifts.
They will ask:
- What controls did you have in place to prevent this?
- How were staff trained and monitored?
- What policies governed data handling?
- How often were these controls reviewed?
- Can you show evidence of management oversight?
Not opinions.
Not assumptions.
Evidence.
And this is where most businesses fall apart.
Why IT Providers Don’t Fix This
Most IT providers are built to deliver:
- Support
- Maintenance
- Tools
They are not structured to deliver:
- Governance
- Compliance oversight
- Risk management frameworks
- Board-level reporting
So even when they do a “good job” technically, the business is still exposed from a compliance perspective.
Because nobody is joining the dots between:
Technology → Risk → Responsibility → Evidence
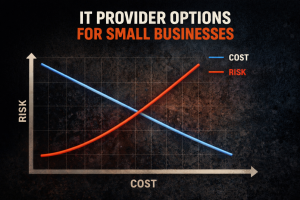
The False Economy of Choosing on Price
This is where the pricing conversation becomes dangerous.
A cheaper provider may:
- Install the same tools
- Respond to tickets just as quickly
- Keep systems running
But if they don’t provide:
- Structured policies
- Risk registers
- Ongoing compliance reporting
- Documented controls
- Strategic oversight
…then what you’ve bought is technical support, not protection.
And when something goes wrong, the cost difference becomes irrelevant.
Because the exposure isn’t technical.
It’s legal. Financial. Reputational.
What Business Owners Should Actually Be Asking
Instead of focusing purely on price and tools, the conversation should shift.
Ask your IT provider:
- How do you help us demonstrate compliance?
- What evidence will we have if something goes wrong?
- How do you document and report on risk?
- How do you ensure ongoing management—not just setup?
- What would we show the ICO tomorrow if we had a breach?
If those questions aren’t being answered clearly, you don’t have a partner.
You have a supplier.
The Real Outcome: Protection You Can Prove
Good IT isn’t about preventing every incident.
That’s unrealistic.
Good IT is about being able to stand in front of a regulator, an insurer, or a client and say:
“We understood the risk.
We put controls in place.
We managed them.
And we can prove it.”
That’s the difference.
Not better technology.
Better accountability.